GoPlus Security Module: Building a Decentralized Security Layer for Web3
On February 21, 2025, the Web3 world experienced a catastrophic event when North Korea’s Lazarus Group orchestrated a sophisticated attack that siphoned approximately 401,000 ETH (valued at $1.1–1.5 billion) from Bybit’s cold wallet. This attack, the largest in terms of financial loss in both internet and blockchain history, inflicted severe damage on Bybit and nearly put many users at risk of asset loss. Shortly after, infini, a project known as a “Web3 bank,” lost over $50 million in another attack. GoPlus believes it’s time to re-examine blockchain security issues and how we address them. We believe these malicious events share a common underlying problem: current blockchain architecture has fundamental flaws that prevent it from becoming a widely adopted financial ledger system. The core issue is:
The Absence of a Security Layer for blockchain
For over a decade, we’ve focused on blockchain consensus, ledger security, and protecting distributed systems from attacks, but rarely addressed user security itself. Some describe Web3 as a “dark forest,” where hackers, users, projects, and exchanges are all equal, following the same rules. However, if we want the real “MASS ADOPTION”, we must consider how to protect “good actors” rather than forcing them to compete with “bad actors” on equal footing. We believe the current blockchain architecture — this “dark forest law” — lacks inherent user protection capabilities. Once users click the send button in their wallet, they cannot recall transactions, even if they’re malicious or fraudulent. This vulnerability to security threats and scams creates a high barrier to entry for blockchain adoption. Meanwhile, sophisticated wallet drainer teams, hackers, and scammers become the biggest winners in this “equal” system. Ordinary users suffer from these malicious scams daily, and even professional exchanges aren’t immune.
Some might ask: “Wouldn’t improving security alerts in wallets and websites solve these problems?” While the market offers various security wallets, security plugins, and even Safe’s multi-signature wallet provides Guard security features, assets lost to theft and scams continue to increase, with the environment and trends steadily worsening. We believe the core issue is that security reinforcement at the UI/UX level is far from sufficient, facing several challenges:
- Cannot solve private key theft issues: UI/UX security reinforcement primarily addresses interface interactions but cannot fundamentally protect private keys. Once keys are stolen through phishing websites, malware, or social engineering attacks, attackers gain complete control of wallets and can send transactions directly to the blockchain without UI/UX interaction. Thus, current security mechanisms cannot prevent malicious transactions initiated with legitimate private keys.
- Defense mechanisms can’t keep pace with evolving attack methods: Security is an endless arms race. Attackers need only find one vulnerability to succeed, while defenders must guard against all possible attack vectors. In the Web3 ecosystem, attack methods innovate rapidly, but security updates and protective measures typically require rigorous testing and review before deployment, creating a time gap that attackers exploit. For example, Ledger wallets cannot identify Safe multi-signature transactions, leaving most users in a “blind signing” state, giving hacker groups ample opportunity to cause significant asset damage before wallets can implement proper support.
- Most Web3 startups cannot match the security standards of professional Web2 companies: Compared to mature Web2 companies with professional security teams and comprehensive security processes, many Web3 projects are driven by small teams or communities lacking professional security resources and experience. Developers focus more on feature innovation than security reinforcement, resulting in inadequate security awareness and practices. In such circumstances, even basic security vulnerabilities are often overlooked, let alone defense against advanced attacks.
- The security lifecycle chain is too long, stretching from Web2 stack to Web3 stack: Current Web3 application security lifecycles span both Web2 and Web3 technology stacks, forming a lengthy and fragile security chain. From user products (Web2) to smart contracts (Web3), each link can become a security vulnerability. This “barrel effect” means security is only as strong as the weakest link. Attackers can target any level, and this fragmented security chain makes comprehensive protection extremely difficult. The Bybit incident exemplifies this, where attackers used JavaScript injection to attack, ultimately resulting in Web3 asset losses.
Therefore, we believe we should reconsider this problem. GoPlus believes the core solutions are:
- Isolating the Web2 and Web3 stacks in the user security lifecycle: The Web2 and Web3 technology stacks are fundamentally different worlds with completely different security models and risk points. When we try to solve Web3 problems with Web2 security thinking, we often address one issue at the expense of another. By establishing a security isolation layer between Web2 and Web3, we can ensure that even if the Web2 layer is compromised (e.g., UI tampering or phishing interfaces), Web3 asset security remains protected. This isolation means transactions must pass through a security check mechanism independent of the Web2 interface before reaching the blockchain. This mechanism is directly integrated into the blockchain’s native layer (sequencer & validator) or RPC layer, not relying on vulnerable frontend interfaces. In the Bybit incident, had such an isolation layer existed, even if attackers successfully tampered with JavaScript files, malicious transactions attempting to change contract addresses would still have been identified and intercepted by the on-chain security layer.
- Building Web3 stack security infrastructure from scratch: The blockchain world needs its own native security infrastructure, not simply transplanted Web2 security solutions. This means redesigning security architecture specifically for blockchain transactions, including on-chain transaction simulation, smart contract risk analysis, and on-chain firewalls. This new security infrastructure should be decentralized, transparent, user-verifiable, and provide real-time protection without compromising transaction performance or decentralization characteristics. Unlike traditional centralized security services, Web3 security infrastructure should maintain blockchain’s core values — openness, permissionlessness, and user autonomy — while providing robust security protection. This requires industry-wide collaboration to establish open standards, share security data, and jointly combat increasingly complex attack methods.
- Implementing user-driven security intent: In Web3’s design philosophy, users have complete control over their data and assets. However, in terms of security, many solutions are either too simple (like simple warning prompts) or too complex (like writing complex security policies). We need to establish a new user security model that allows users to express their security preferences and intentions in a simple, intuitive way, then have intelligent systems translate these intentions into complex security policies and automatically settle them. For example, users could simply express “I want to avoid interacting with contracts marked as risky” or “I want additional confirmation for transfers exceeding X amount” without understanding the underlying technical details. This user-driven security model places users’ security intentions at the core while not increasing operational complexity, truly achieving “security as a service.” Ultimately, users have the right to enable or disable security protection, which will take effect at the chain’s native layer.
Here, we’d like to introduce our solution — GoPlus Security Module (GSM)
What is the GoPlus Security Module?
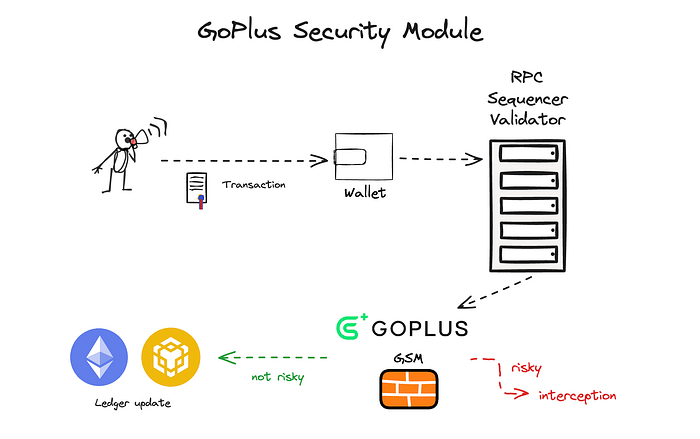
GoPlus Security Module (GSM) is a key component in GoPlus’s core architecture, designed to address security challenges in the Web3 environment. It’s a software development kit (SDK) that can be seamlessly integrated into various Web3 scenarios, including wallets, dApps, RPC nodes, and even Layer 2 sequencers.
GSM’s core function is to serve as a bridge between user-initiated transactions and GoPlus’s security services. When a transaction is triggered, GSM obtains the transaction data and forwards it to the GoPlus security service network. The GoPlus network evaluates transaction risk in real-time using advanced AI algorithms based on the transaction and the user’s pre-configured security intentions. The risk analysis results are then returned to GSM, which can take appropriate action according to security recommendations, such as allowing safe transactions or rejecting malicious ones.
Unlike traditional Web2 security solutions, GSM is built directly at the blockchain level, forming a security isolation layer between on-chain and off-chain. This approach avoids dependence on Web2 security infrastructure, fundamentally solving the “barrel effect” problem — where a security system’s strength is determined by its weakest link. By establishing an independent security module on-chain, GSM ensures that user assets and transactions remain protected even if Web2-level UI/UX has security vulnerabilities.
GSM features include:
- Modular design: As an independent user security and risk control module, GSM can be seamlessly integrated into various modular blockchain architectures.
- Multi-chain support: GSM is designed to adapt to multiple blockchain networks, providing a consistent security layer across different ecosystems.
- On-chain risk management: Utilizing AI algorithms and security engines provided by the GoPlus network, GSM can quickly analyze and mitigate transaction risks in real-time.
- Customizable security strategies: Allows users to customize security preferences based on personal risk tolerance and needs.
- Seamless user experience: Provides a secure environment for Web3 users without requiring them to become security experts.
- On-chain security isolation: Builds security barriers at the blockchain’s native layer, not relying on vulnerable Web2 security infrastructure.
- Inherent decentralization: Uses a decentralized security verification network based on AVS architecture, ensuring the security mechanism itself doesn’t become a single point of failure, allowing anyone to participate in security computation, contribute security data, and receive corresponding incentives.
Through these innovative solutions, GoPlus Security Module provides each chain with an on-chain firewall directly integrated into the blockchain. This firewall automatically filters transactions according to users’ personalized security policies, blocking risky transactions in real-time at the RPC level or in integrated chains. This ensures that blockchain interaction security becomes an inherent part of the user experience, achieving seamless and secure blockchain interaction.
Specific implementation and advancement through collaboration with chains includes three stages:
- GoPlus Intelligence integration: The GoPlus network provides tailored GoPlus Intelligence support for specific blockchains, including real-time transaction security insights and risk assessments.
- Secure RPC service: Deploy secure native RPC nodes that users can directly use for enhanced protection.
- Native blockchain integration: Collaborate with blockchain projects to directly integrate the user security module into the blockchain architecture, making security checks an inherent part of the transaction validation process.
- Personal security center: Enable support for new chains in the personal security center provided by GoPlus, where users can manually enable corresponding security risk preferences.
GSM’s Impact on Chain Performance and Decentralization
GoPlus Security Module’s design fully considers its impact on blockchain performance and decentralization characteristics, achieving a balance between security, performance, and decentralization:
Performance Impact
GSM employs a lightweight design to minimize its impact on chain performance:
- Efficient computation: GSM uses optimized algorithms and efficient data processing to ensure security checks complete at the millisecond level, with negligible impact on transaction confirmation times.
- Distributed computation: Through AVS architecture, security computation workloads are distributed across multiple operator nodes, avoiding single-point performance bottlenecks.
- Intelligent filtering: GSM doesn’t subject all transactions to the same level of scrutiny but dynamically adjusts resource allocation based on risk assessment, conducting deeper checks on high-risk transactions.
- Intelligent caching and detection acceleration: GSM caches intermediate results and pattern recognition components of risk detection, such as smart contract security analysis results, address risk scores, and common attack pattern features. These data remain relatively stable in the short term and can be reused to accelerate detection processes for subsequent related transactions, similar to traditional financial systems’ risk control mechanisms.
Actual tests show that GSM typically adds around 200 milliseconds to transaction processing time, which has negligible impact on overall blockchain performance, especially considering most blockchains have block generation times of seconds or longer.
Decentralization Characteristics
GSM’s design actually strengthens blockchain’s decentralized nature while providing protection against Web2 interface vulnerabilities:
- Open participation: Anyone can participate in the network as a data provider, compute node operator, or SecWare developer.
- Decentralized governance: Key decisions are determined through decentralized voting mechanisms, including protocol upgrades, parameter adjustments, and dispute resolution.
- Transparent incentives: All participants receive transparent, verifiable incentives based on their contributions, avoiding centralized control.
- No privileged nodes: The network has no nodes with special permissions; all operators are technically equal.
- Open-source code: Core components are open-source, ensuring transparency and community audit capabilities.
- On-chain security independence: GSM’s security mechanisms run directly on-chain, independent of vulnerable Web2 interfaces; even if frontend UI/UX is compromised, on-chain security remains unaffected.
In fact, GSM brings a higher level of security protection to blockchains without sacrificing decentralization. It follows the “security as a service” paradigm, providing an additional security layer without altering underlying blockchain architecture or consensus mechanisms, while addressing risks from Web2 security vulnerabilities in current Web3 applications.
GSM’s Significance and Technical Innovation for On-Chain Ecosystem Security
The launch of GoPlus Security Module marks a paradigm shift in blockchain security, not only solving current security challenges but also bringing profound implications for the entire Web3 ecosystem:
Technical Innovations
- Security layer standardization: GSM establishes a new standard for blockchain security, transforming security from reactive remediation to preventive protection. It creates a standardized security interface implementable across different chains and applications.
- Decentralized security network: Builds the first truly decentralized on-chain security network, integrating data provision, security computation, and risk defense, breaking the centralized model of traditional security services.
- On-chain firewall concept: Introduces the blockchain world’s first “on-chain firewall” concept, similar to the firewall revolution in the internet world, providing real-time protection mechanisms for Web3 users.
- Web2-Web3 security isolation layer: Innovatively builds a security isolation layer on-chain, making blockchain transaction security independent of vulnerable Web2 interfaces and infrastructure, fundamentally solving the “barrel effect” problem.
- AI-driven security analysis: Applies advanced AI technology to on-chain transaction analysis, identifying complex and evolving attack patterns that manual rules cannot capture.
- User-driven security model: Innovatively returns security control to users, allowing personalized security policies, changing the traditional “one-size-fits-all” security approach.
Current Status
- Coverage: GoPlus already supports over 30 blockchain networks, handles 30 million API calls daily, has scanned over 10 million tokens, and processes over 100,000 transactions daily.
- Deployed features:
- Secure RPC services are live on ETH and BNB chains
- GoPlus APP has launched, serving over 28.4M wallet users
- GoPlus Extension has launched, with over 250k users
- Over 5000+ partners have integrated GoPlus Intelligence API
3. Technical maturity:
- Core security detection engine market-validated
- Decentralized computing architecture implemented based on EigenLayer’s AVS
- Security data layer transitioning from centralized to decentralized
4. Partnership ecosystem: Established partnerships with mainstream wallets (Trust Wallet, TokenPocket, OKX Wallet, Binance Web3 Wallet, etc.), price tracking sites (CoinGecko, CoinMarketCap, Dexscreener, etc.), and DEXs (SushiSwap, etc.).
GoPlus’s vision is to build Web3’s standard security layer, providing comprehensive protection for all blockchain networks. Through modular, decentralized, and user-driven methods, GoPlus Security Module aims to redefine the future of blockchain security, making the security layer a natural component of the Web3 experience.
